The Rise of Theft Lock and other Keyed Modules & How it impacts Service
- Tyler Betthauser
- 4 days ago
- 6 min read
Updated: 3 days ago
Original Equipment Manufacturers (OEMs) have increased their focus on cybersecurity as vehicles become more data intensive, connected, and automated. With more threat vectors than ever, software engineering teams have implemented security measures that can have significant consequences for the aftersales groups tasked with servicing these vehicles. One of the most prominent consequences is the theft lock. This state occurs when a module becomes unusable because of a mismatch between the unique identifier stored in its internal memory and the one stored in a secondary module that validates authenticity. When a mismatch is detected, the vehicle usually alerts the driver through a display message or by disabling specific features. This article describes the design of the theft lock mechanism, its impact on serviceability, and what you need to know about how these protocols affect the repair process.
Why Theft and Cyber-Locks Exist
While these cybersecurity features can make servicing vehicles more difficult and specialized, there are functional reasons for their usage. During my time in infotainment engineering, the most cited reason for these protocols was data protection. Modern vehicle software stores personal information that an attacker could use to steal an identity or impersonate a driver. This data includes contact information, (sometimes) precise location history, and even purchase records (think saved credit card information for faster purchasing). By implementing a theft lock, manufacturers ensure that a stolen or salvaged Electronic Control Unit (ECU) cannot be swapped into another vehicle to gain access to the previous owner's sensitive information.
Beyond individual privacy, these locks protect the integrity of the vehicle's internal communication systems. Certain modules interact directly with the Controller Area Network (CAN) and Ethernet backbone of the car. An ECU that has not been authorized or authenticated with the proper digital certificates cannot be trusted on the network. Without these barriers, an unauthorized party could potentially modify the software to alter the car's physical behavior. This vulnerability was famously demonstrated in 2015 when security researchers Charlie Miller and Chris Valasek remotely took control of a Jeep Cherokee through its Uconnect infotainment system. By exploiting a cellular connection, they were able to manipulate the vehicle's steering, transmission, and braking while it was traveling on a highway. This event triggered a recall of 1.4 million vehicles and forced the entire industry to move beyond simple perimeter security toward the zero-trust network architectures that necessitate component locking today.
The conversation around these locks often focuses on the drawbacks for the aftersales market or the perception of planned obsolescence. While it is true that these implementations make third-party repairs more difficult, the core intent is not always to force a new vehicle purchase or make vehicle ownership impossible. Serviceability is an inherently complex problem for large manufacturers because of competing internal interests. In large automotive organizations, these consequences are often the byproduct of misaligned incentive structures. A cybersecurity team is tasked with ensuring the vehicle cannot be breached, so they implement rigorous cryptographic handshakes and server-side authentication. Meanwhile, the service engineering team is focused on minimizing repair complexity and costs. Because security requirements are often driven by legal compliance and safety standards, they tend to take precedence during the development cycle. Serviceability becomes a secondary concern. This results in a scenario where the security protocol is technically sound from a defensive standpoint but creates significant hurdles for a technician in the field who lacks access to proprietary OEM servers.
How do Theft and Cyber-Lock Systems Work?
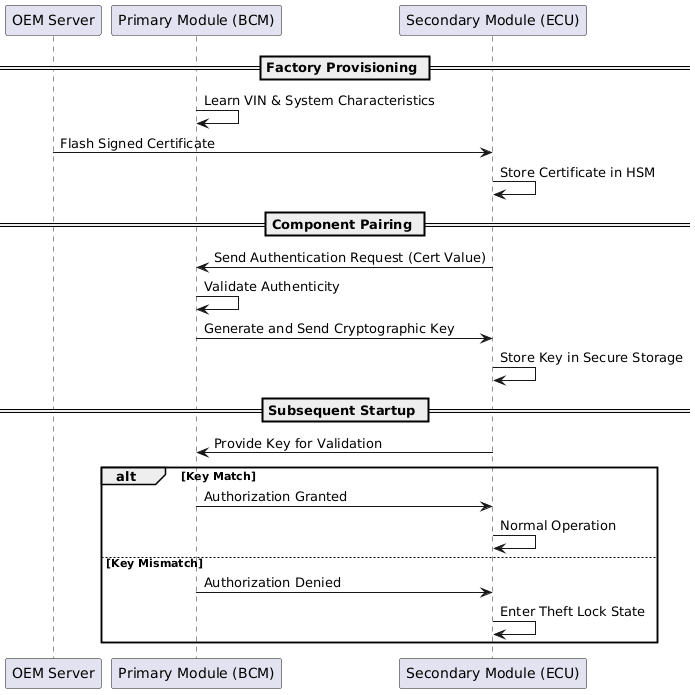
Depending on the electrical and software architecture, manufacturers may accomplish certification and authentication tasks differently for each ECU on the network. While previous discussions have explored domain-centralized and centralized systems, the core concepts of component locking generally apply to both. We talk about these architectures here: When the Dashboard Goes Dark: The Car Conservatory’s Guide to Digital Failure. These systems typically follow a primary and secondary pattern to distribute the cryptographic keys used to verify the legitimacy of a module.
The primary module is often the Body Control Module (BCM) or a central Gateway. The BCM is an ideal candidate for this role because it manages the Vehicle Identification Number (VIN) and coordinates various non-propulsion features. Furthermore, the BCM is generally difficult to access physically, which acts as a secondary deterrent against tampering. The secondary modules include any other components on the network that require authentication, such as the infotainment system or the Transmission Control Module (TCM). Within the software of the primary module, a Hardware Security Module provides a secure environment where seeds and keys are stored. Secondary modules possess a similar setup to ensure that even if the hardware is accessed using a debug board, the cryptography remains difficult to breach.
The pairing process begins at the manufacturing plant. When the primary module is installed, it learns the VIN and other identifying characteristics. As secondary modules are added, they undergo a programming event where they receive a signed certificate from a central OEM server. This certificate is flashed into the secure memory location of the module. This step is permanent and cannot be reversed unless a technician uses a scan tool capable of communicating with OEM servers to initiate a re-pairing process. This specific requirement is a central point of contention for right to repair advocates.
Once the initial flashing is complete, the system establishes the cryptographic key. A message is sent over the CAN or Ethernet bus between the modules to provide a value from the certificate to the primary module. This validates that the device is authentic. The primary module then responds with a key that is stored in the secondary module. On every subsequent startup, the secondary module provides this key to the primary module. If the keys do not match, the module enters the theft lock state described in the introduction, disabling itself until it is reprogrammed with a new signed certificate.
The Trouble of Competing Incentive Structures
While it is technically possible to design secure vehicle networks that remain serviceable for the owner, the internal incentive structures of large manufacturers often prevent this outcome. Aftersales departments are frequently tasked with building infrastructure that ensures drivers return to authorized service centers. This objective is often achieved by making the acquisition of programming tools and software licenses cost-prohibitive or entirely unavailable to anyone outside the dealership network. This creates a functional barrier that reinforces the exclusivity of the dealer model.
Conversely, many within engineering and software development would prefer that systems and tools be accessible to the end user. However, these voices are often overridden by legal departments. These legal teams are sensitive to the influence of dealer associations, which are often the most powerful political donors in their respective states. Because these associations wield significant lobbying power, corporate leadership—including middle management and junior directors—is often hesitant to rock the boat.
This tension was highly visible during the introduction of OTA updates at Ford and General Motors. The core of the legal battle was not just about the technology itself, but about whether a remote software flash constitutes a warranty repair. Under most franchise agreements, a warranty repair requires a payout from the manufacturer to the dealer. By bypassing the physical service bay, manufacturers threatened a major revenue stream for dealerships. Lobbying and lawsuits follow when these exclusivity agreements are undermined. This resulting organizational gridlock is where much of the speculation regarding planned obsolescence and conspiratorial design begins to take root.
Bring Your Vehicle to Shops that Will Prioritize the Technology
Most drivers will not invest in the specialized tools and software subscriptions required to service their own vehicle. This reality makes the choice of a repair facility critical. Unfortunately, many independent shops hesitate to invest in the technology necessary to handle modern ECU replacements. When a shop lacks these capabilities, they are often forced to sublet the work to a dealership or another specialist. This limitation adds significant time to the repair and introduces a broken chain of custody. Every time a vehicle is transported between facilities, the risk of transport damage increases and liability becomes blurred if a programming event fails. For the customer, this means a simple part replacement can turn into a multi-day ordeal with multiple points of potential failure.
To avoid these pitfalls, owners should seek out facilities that prioritize diagnostic technology. Modern tools like those from Autel act as a technical bridge across the digital fence created by manufacturers. These devices allow technicians to perform remote programming without requiring individual, high cost licenses for every manufacturer back office. By using these bridges, an independent shop can maintain control over the repair process from start to finish, ensuring the vehicle remains secure and the theft lock state described in the introduction is resolved efficiently. While these hurdles are frustrating for the independent aftermarket, they provide a modicum of protection by ensuring that programming events are authenticated and the vehicle's data integrity is preserved.
There should be an 'Open Source' Solution Provided
Repair shops should not be the sole gatekeepers for vehicle service. Owners who prefer to maintain their own vehicles should be empowered with the same digital tools as professional technicians. Technically simple solutions could exist to provide certificates and software at a reasonable cost. For example, manufacturers could provide branded portals where drivers prove their ownership through digital titles or multi-factor authentication. Within such an account portal, a user could download signed certificates directly to a flashing device and access the most recent software updates for their specific VIN. By providing a legitimate path for owners to resolve a theft lock state, manufacturers would move away from the closed-loop system that currently defines the aftersales experience.

Get the Best Care for your Car
If you want a repair experience unlike any other, get an estimate now!



Comments